Secure Data Room Software Guide for 2025
Explore the enterprise guide to secure data rooms in 2025. Learn use cases, essential features, and how Pydio Cells delivers control, compliance, and...
Your teams need the right tools to work effectively. But those tools can’t put the organization’s security at risk. Enterprise SaaS solutions put someone else in control of your data. Fully self-hosted and private/hybrid cloud-ready, Pydio Cells provides the seamless sharing, collaboration and management your teams need without security or compliance trade-offs.

Here are 6 factors that set us apart from the competition and make Cells the right choice for security-conscious organizations.
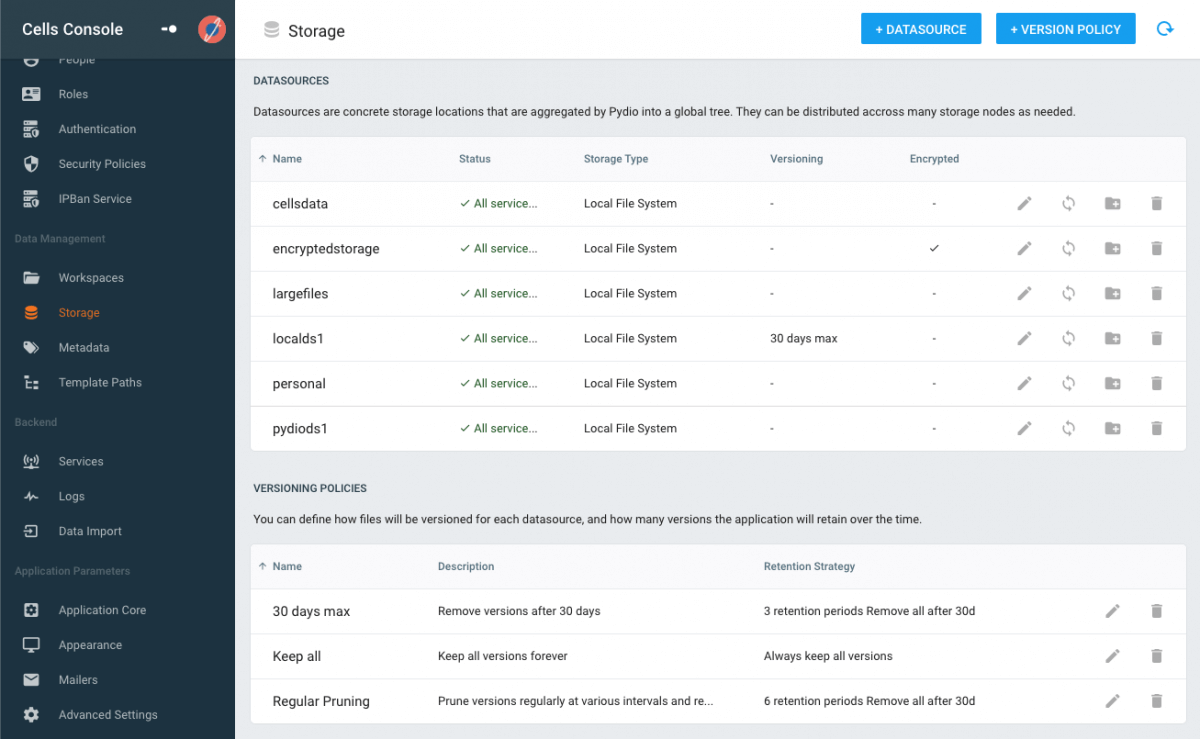
Whether in your own data centers on your own servers, in your own private Cloud, or a hybrid of both, you can ensure your storage is compliant to your internal policies.
Your data is encrypted at rest, and all communications are secured via SSL.
SSO is handled simply and securely via a proven protocol that integrates easily with Open ID Connect, OAuth2, and SAML.
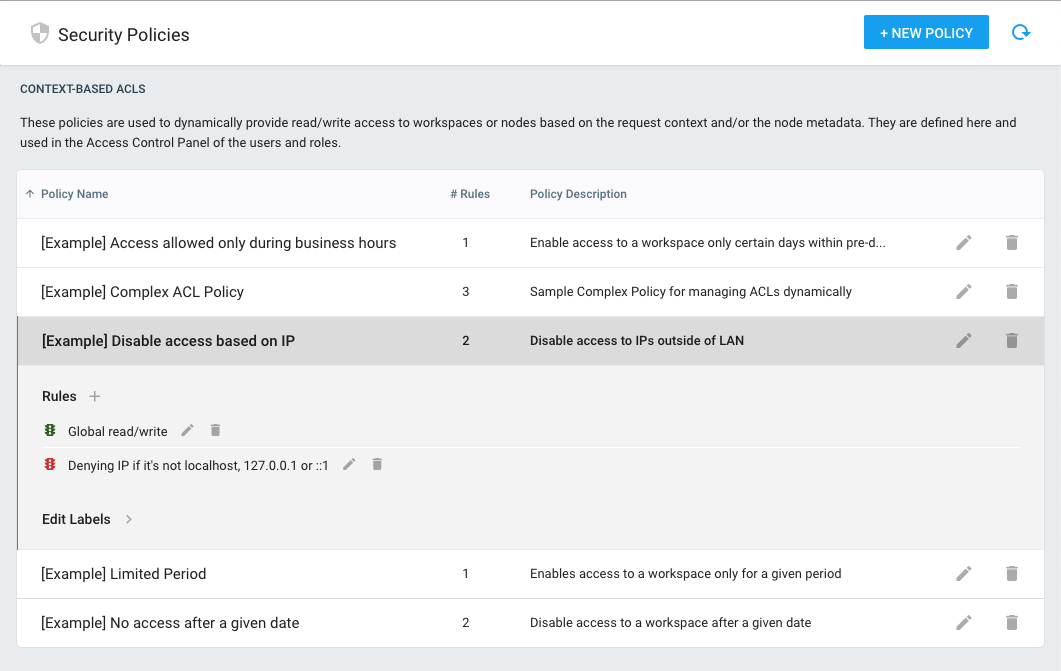
Programmable Security Policies allow you to implement programmable access rules (ACL) needed to comply with regulations and to your own data governance practices.
With in-depth log management & audit tools, your application delivers detailed technical & activity logs in standard JSON format. Logs are then aggregated and easy to parse with modern logging tools like ELK. In addition, you can also export logs in XLSX/CSV formats to integrate with platforms.
Pydio includes AD & LDAP attribute mapping, making it easy to apply your existing access rules to your Pydio instance. You can also connect to several LDAPs.
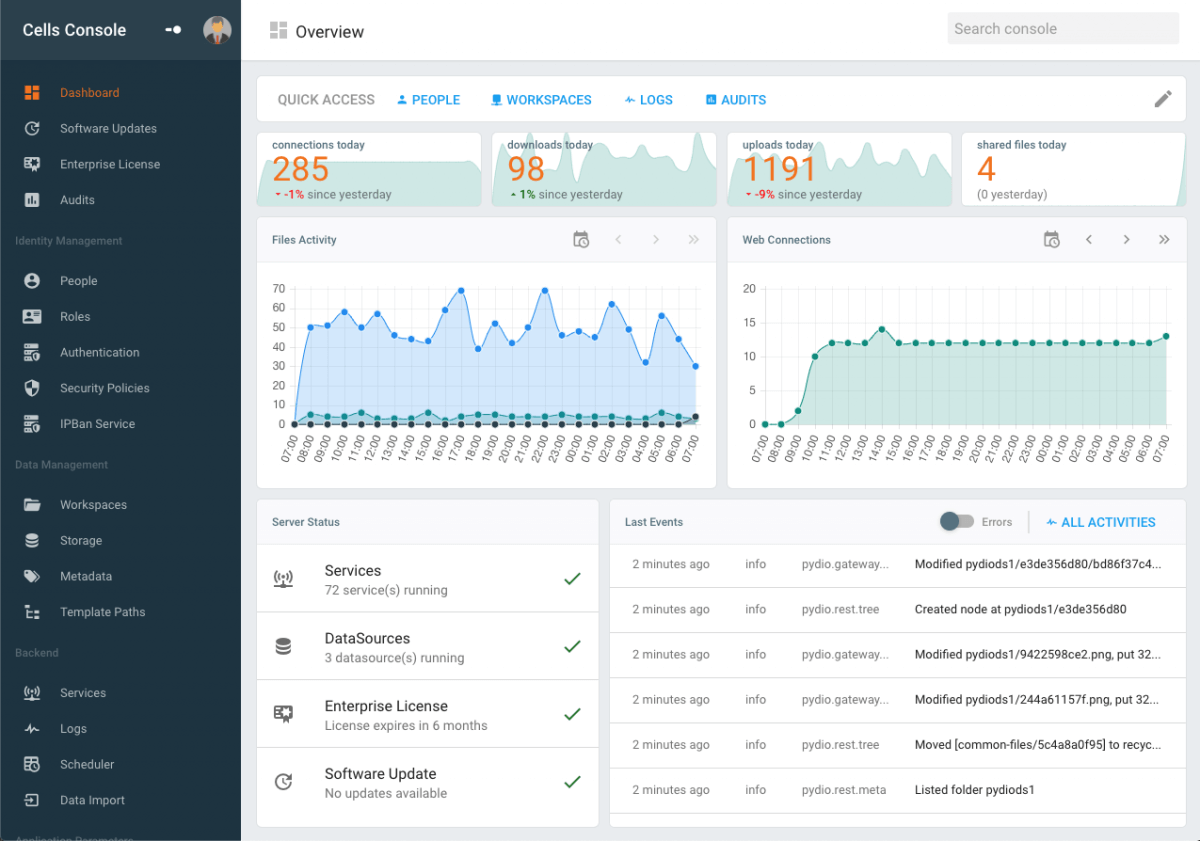
Our powerful Admin Dashboard provides rapid access to in-depth security reporting features.
For added protection, configuration changes are all logged, and a differential can be easily displayed.
Logs are stored in JSON to facilitate integration with modern logging platform.
Pydio helped us solve many regulatory compliance issues. We needed a fast-to-deploy on-premise solution to allow auditable file exchanges with our customers and Pydio really fits the bill. Pydio's premium remote support was the cherry on the cake.
We've been using Pydio for years now and the platform has always met our needs for end user experience and advanced security. Today we have more than 10 Pydio instances and they are at the heart of our customer data exchanges. Moreover, GDPR has strengthened our desire to control our data and Pydio responds very well to this need.
We’ve been using Pydio Cells at CY Cergy Paris Université as a sovereign solution for our research staff since early 2019. Following the increased need for collaboration during the Covid19 crisis, we opened the tool to all university staff. It meets our needs very well and is easy to learn. The granular access management via the 'Cells' concept is very flexible and efficient.
We provide Level 3 support for enterprise clients, with rapid troubleshooting when an incident is logged. Enterprise support includes:
We also offer a Premium Remote Support package that covers remote installation, migration, upgrades, performance optimizations, and custom code debugging.

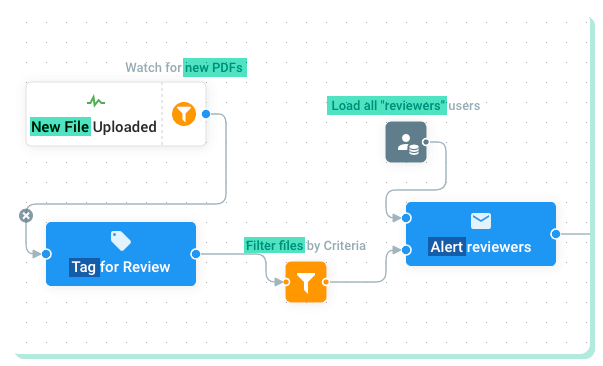
Pydio Cells Flows is a powerful new tool that lets you assemble customizable components via a drag and drop interface to automate repetitive, time-consuming tasks that are a drag on productivity and your bottom line.
Want to stay up to date with everything Pydio? That’s easy. Just subscribe to our newsletter or follow us on LinkedIn.
.png?width=960&name=Oliver%20blog%20(24).png)
Explore the enterprise guide to secure data rooms in 2025. Learn use cases, essential features, and how Pydio Cells delivers control, compliance, and...
.png?width=960&name=Oliver%20blog%20(23).png)
Explore the complete guide to ECM software. Learn how enterprise content management works, what features to look for, and how to select the right ECM...
.png?width=960&name=Oliver%20blog%20(19).png)
Compare top EFSS platforms, explore security features, deployment options, and find the ideal enterprise file sharing solution in 2025. Make informed...
Do you need more information about the product? Looking for a specific feature or a formal quote? Leave us a message!