Our client, Dekra, is a leading provider of inspection, certification, and claims management services to the automotive, transport and industrial sectors. They collaborate with an extensive network of agents to gather inspection and certification data.
The client came to us looking to implement their pre-existing (and quite complex) OpenID Connect directory permission model within Pydio Cells. The shared data is composed of a huge number of folders that all share the same subfolder layout. Users are granted access to these subfolders using role-based permissions.
“As a starting point, we were looking to reduce the amount of email and admin work being generated. But we also wanted to streamline time consuming workflows and our existing infrastructure couldn’t bridge the gap between our internal systems and the systems our partners and their clients use. Pydio Cells addressed this challenge for us and has gone on to help accelerate customer service and improve productivity.”
Nicolas Bauchet - Manager, Digital Solutions and Innovation, Dekra
Main Challenges
-
Interpret the “encoded” entitlements from the client directory and translate them into Pydio-readable permissions for specific data paths
-
Apply these permissions for each user to allow access to specific folders and subfolders
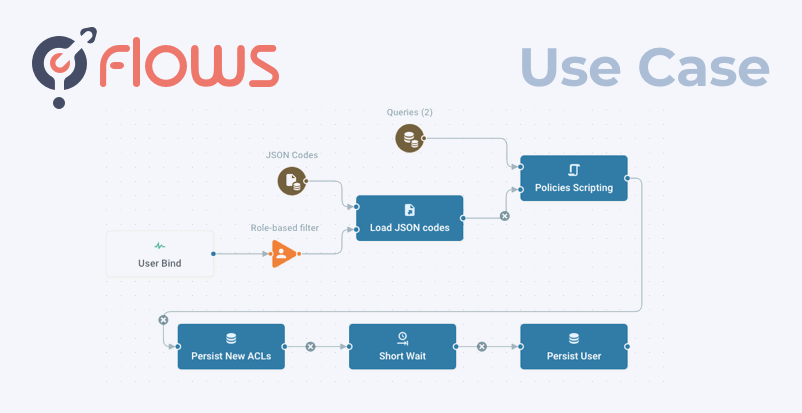
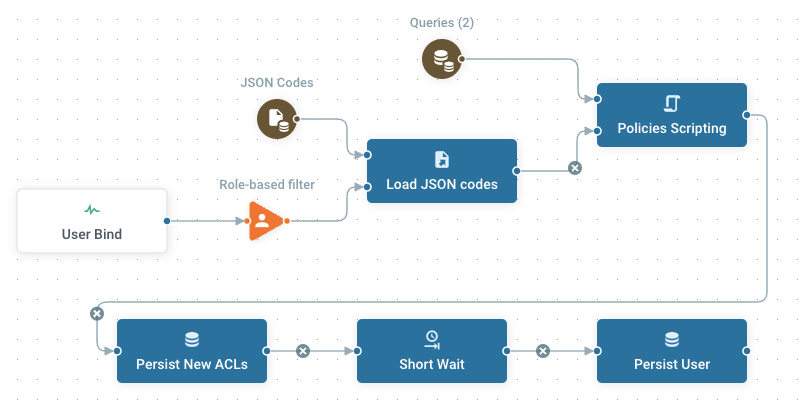
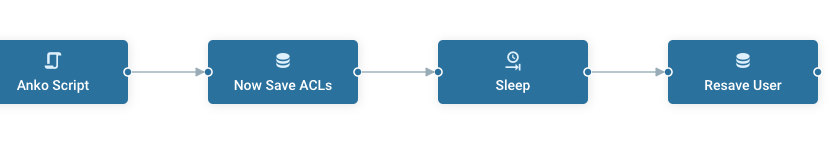
Flow Map
Implementation
1 - Decode “Entitlement” to Create an Authorized Path
At login time, the OIDC provider sends back a User with a list of entitlements that encode specific data in a format like GROUP_CodeSite_Year_Role. Each part represents a level in the folder tree, either directly (Year 2022 => folder ../2022/…) or indirectly (CodeSite refers to an external list associating Codes => Site Names). The Flow needed to account for five different types of variable in its encoding.
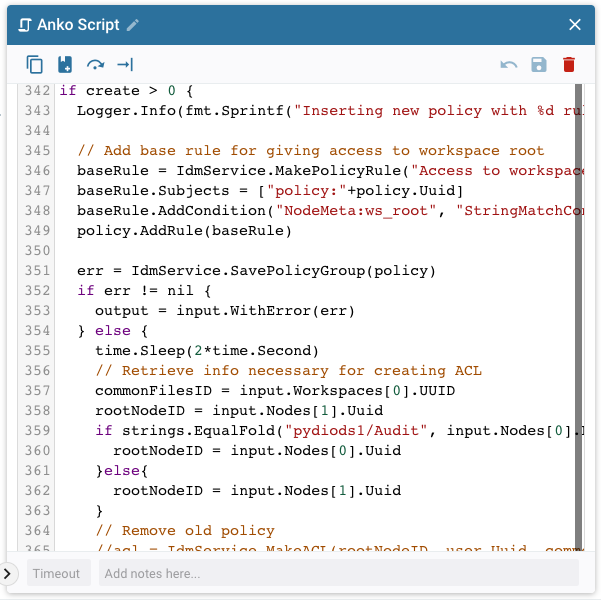
Scripting capabilities
Using an “Anko” action, we used pseudo-GO code to read all user roles and apply various string splits and transformations.
Injecting additional data for CodeSites
As explained above, the Flow required an external set of data to translate a “CodeSite” into a proper Site Name (and folder name). For that, we simply store this list as a JSON-encoded file in Pydio Cells (in a protected Cell), and let the Flow load its content and pass it as JSON as an input to the Anko action.
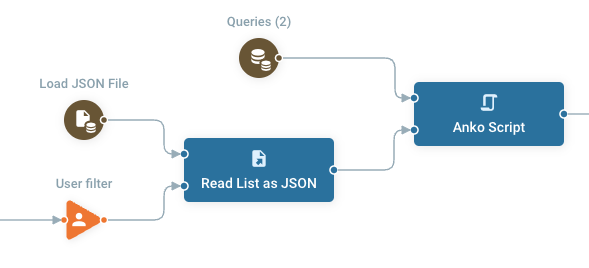
With that, and the precise client requirements for implementing the decoding rules, we had the tools to decode the input.
2 - Apply Dynamic User Permissions
Once we had the tool to “understand” the OIDC entitlements, we needed to decide how to apply permissions to grant access.
There were multiple possible approaches to this challenge. The typical solution is to create workspaces (that point to a specific location) and grant access to them on the fly. But in this case, that approach would lead to the creation of a vast number of workspaces for each user. Instead we chose to create on-the-fly security policies that “filter” the visible/editable contents of a unique, shared workspace, and assign these policies dynamically to each user.
Security policy creation is done directly inside the Anko script and ACLs are assigned to users in the script as well, and saved afterward in a separate action.
Impact
As a result, when users log in to the platform, their permissions are dynamically assigned and eventually refreshed if there are changes to the directory, providing admins with fully centralized permission management while keeping data access fully secure. This allows our client to integrate Pydio Cells into their core workflows to accelerate sharing and collaboration on key documents.
Put Flows to Work for You
This article focuses on several features of the Flow being described but it is not a how-to. If you’d like to learn more, contact one of our Flows experts.