Cells for Defense & Law Enforcement
Defense organizations and law enforcement agencies need to share documents and collaborate just like any business. The difference is the level of control and security required and the complex web of processes, procedures, regulations and standards they need to comply with.
Cells is designed to meet the stringent demands of defense and law enforcement agencies. Multiple military branches and law enforcement agencies in Europe and North America already use the platform. Whether it's sharing intelligence reports or managing confidential investigations, you can rely on Cells to safeguard your critical information and empower your teams to excel.
Military-grade Security
-
Install Pydio in a firewalled environment with direct access restricted to inner-company users. Your data stays on your storage and is managed by you, and only you.
-
Your data is encrypted at rest, and your exchanges are protected with Secure Socket Layer (SSL) and Transport Layer Security (TLS) protocols.
-
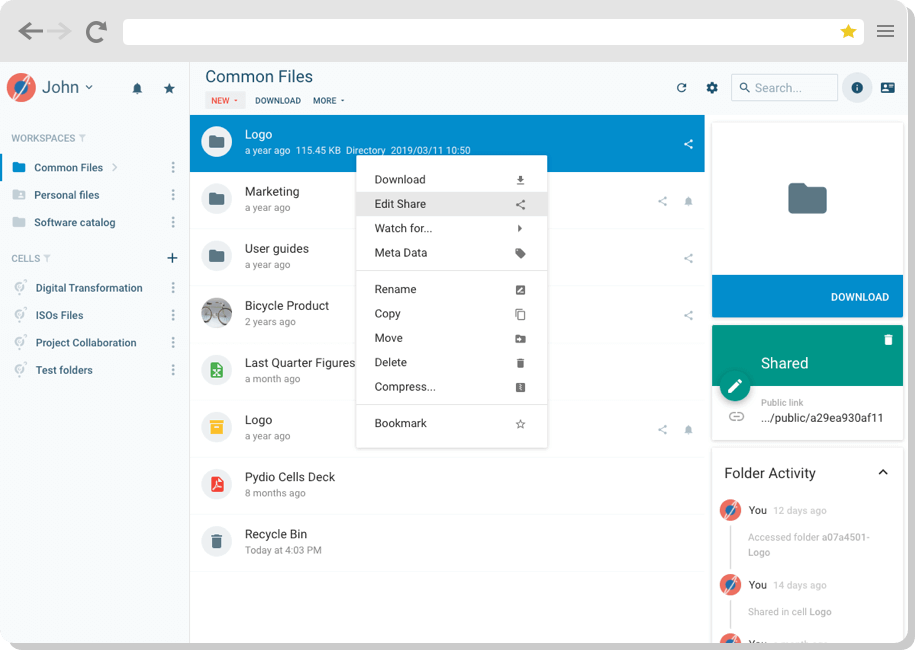
Secure public links with a password, set a maximum number of downloads or date-based automatic expiration, and monitor when external partners access links.
We care what our customers think of us and so should you. We are partners in your business and your success is ours.
It’s no surprise that our needs for sharing and collaboration come with serious security requirements. Pydio lets us share documents efficiently within our teams and with approved partners without putting that data at risk. And that is mission-critical for us.
Manage and Control Your Files Efficiently
-
Set up secure, access-limited Cells as needed and improve your workflows through centralized file access.
-
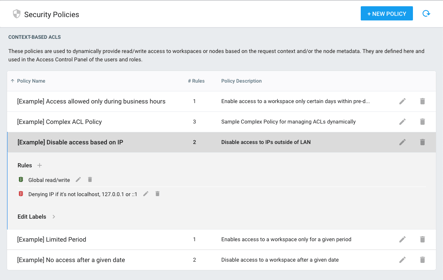
Set individual user access permissions, and manage rights access at a granular level. Permissions can be set at a group, role or user level.
-
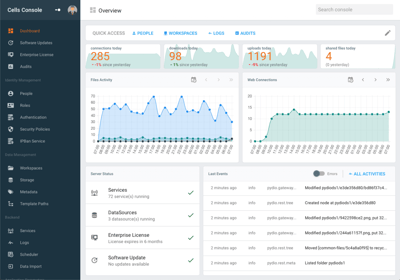
Track system access and activity in real time: get detailed metrics, set up alerts and email notifications, and interrupt any suspicious or unwanted sessions.
Strong Knowledge Management Capabilities
-
All the knowledge your organization generates is only helpful if you can find and leverage it among the tens or even hundreds of thousands of documents you produce annually.
-
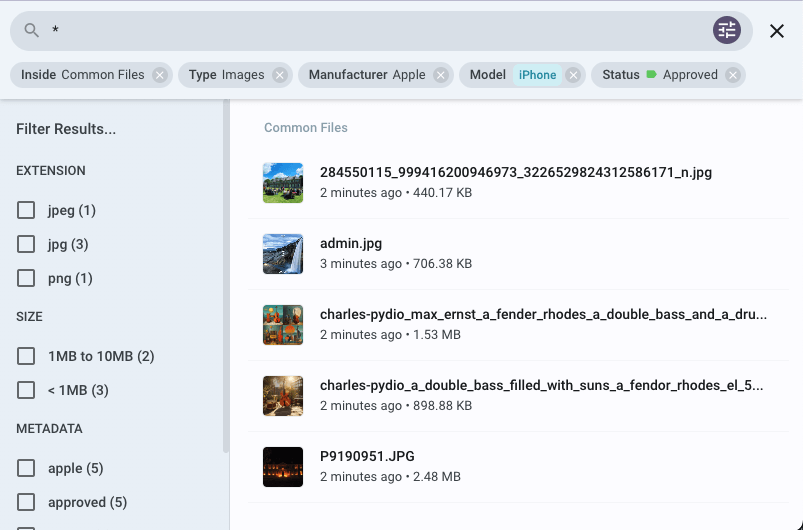
Implementing an automated knowledge management taxonomy that structures the creation of new Cells (think of them as folders) and the documents within those Cells, so each new Cell and document is findable from minute one.
-
Cells’ flexible metadata allows users to create, customize and even automate the completion of metadata fields to ensure your digital assets are findable and manageable.
-
Powerful search functionality now includes NLP-powered assisted search to provide helpful suggestions on search terms. And Cells can search across all of your connected document storage.
Read up on Cells as a Knowledge Management platform here.
Talk to a Pydio Expert
Do you need more information about the product? Looking for a specific feature or a formal quote? Leave us a message!